DarkComet Trojan virus, Remote Access Trojan (RAT) attack on Macintosh
Message from Trojan (RAT). If you see below message in your system you are infected
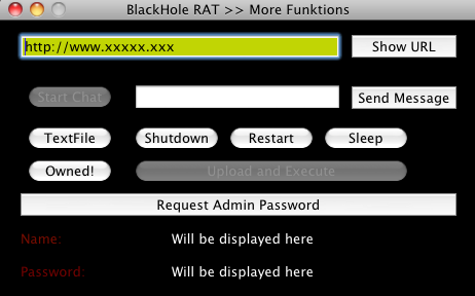
Appears to be a mix of German and English in the user interface. Its functions include:
Download Antivirus here
Hello I'm the BlackHole Remote Administration Tool. I'm a trojan horse, so I have infected your Mac Computer. I know, most people think that Macs can't be infected, but look, you ARE infected! I have full controll [sic] over your Computer and I can do everything I want, and you can do nothing to prevent it. So, Im [sic] a very new virus, under Development, so there will be much more functions when I'm finished. But for now, it's okay what I can do. To show you what I can do, I will reboot your Computer after you have clicked the Button right down.
Appears to be a mix of German and English in the user interface. Its functions include:
- Placing text files on the desktop
- Sending a restart, shutdown or sleep command
- Running arbitrary shell commands
- Placing a full screen window with a message that only allows you to click reboot
- Sending URLs to the client to open a website
- Popping up a fake "Administrator Password" window to phish the target
Download Antivirus here